Video Protection
Protect your videos using expiry URLs, geo-blocking, and whitelisted websites
Gumlet lets you layer multiple protection options to control who can watch your videos, where they can watch from, and for how long. Start with simple privacy controls, then add geo‑blocking, referrer whitelisting, and finally signed URLs if you need maximum security.
Gumlet's video protection works well with workspaces. All the videos inside the workspace will follow the security protocols configured at the workspace level. The security settings are available in your workspace settings.
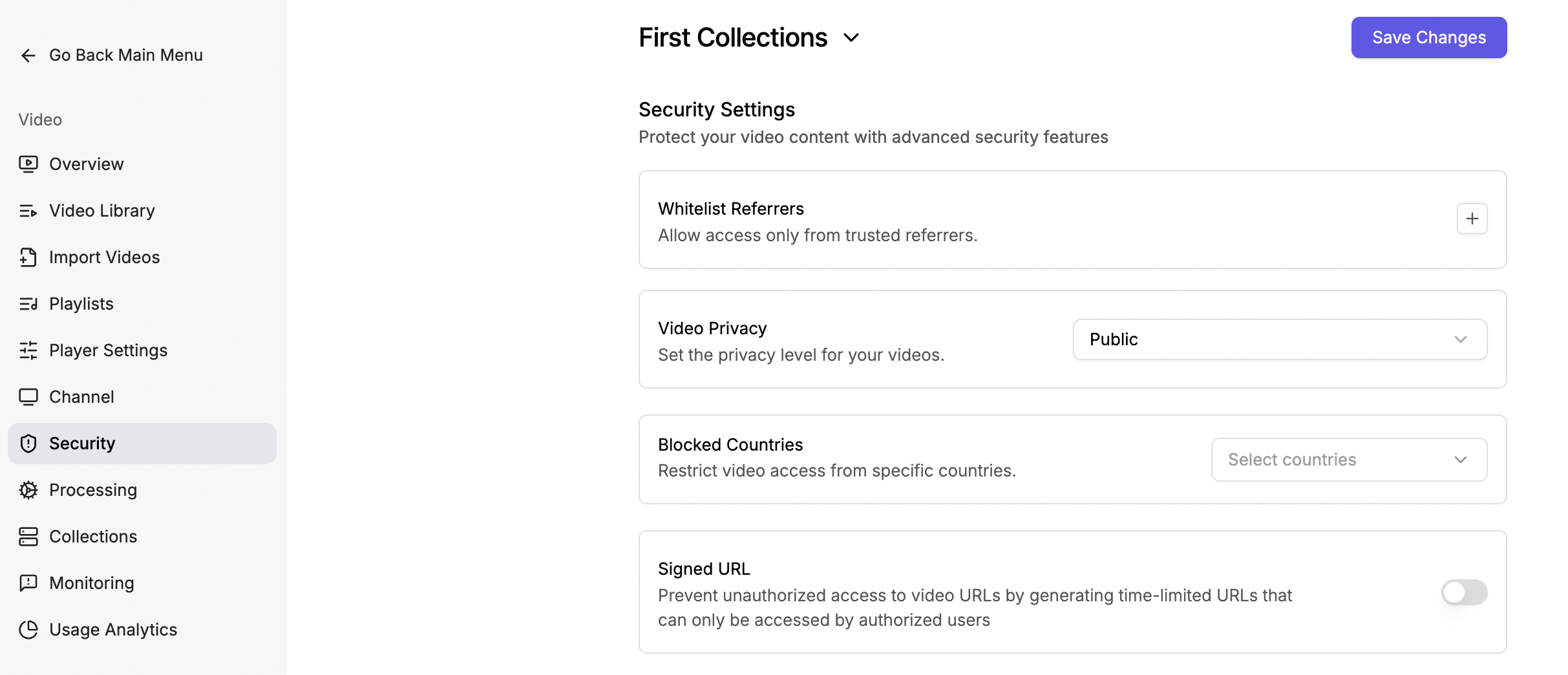
Secure video playback on the collection level.
Available Video Playback Security Options
We recommend starting with privacy, then adding geo‑blocking, referrer whitelisting, and finally signed URLs for advanced use cases.
Use this guide to quickly decide which protection option to use for your videos.
| Option | What it controls | Best for | Example use case |
|---|---|---|---|
| Video Privacy | Who can see or find the video | Basic visibility and link‑based access | Make marketing videos public, course content unlisted or private, demos password‑protected |
| Geo‑blocking | From which countries is playback allowed | Regional or compliance‑based restrictions | Allow only IN and US viewers, or block a few restricted countries while allowing the rest |
| Allow Referrers | On which sites or apps can videos be played | Locking playback to your domains and apps | Allow playback only on example.com, app.example.com, and your mobile apps |
| Signed URL | Who can watch and for how long per URL | Per‑user, time‑bound, or paywalled access | Generate a 1‑hour link for paid customers, revoke access by letting URLs expire |
Video Privacy
Mark your videos as public, private, unlisted, or password-protected.
Public
The public status indicates that videos are publicly playable and can be indexed by search engines.
Unlisted (this is the default)
These videos are unlisted. These are available only when the link is shared.
Private
The private videos play only inside the Gumlet dashboard. To share these videos, change the privacy settings.
Password-Protected
Add a password to your videos to make them bulletproof. The embedded videos also require a password to play.
Geo‑blocking
Geo‑blocking lets you control where your videos can be watched by allowing or blocking playback from specific countries or regions. Use it to comply with licensing rules, regional rights, or to keep content limited to your target markets.
How does geo‑blocking work?
When a viewer tries to watch a video, Gumlet checks their IP‑based location and applies the geo rules configured at the workspace or collection level. If their country is not allowed (or is explicitly blocked), playback is denied even if they have the correct video link and referrer.
Allow Referrers (Whitelisting domains and apps)
The Referer HTTP request header contains the absolute or partial address of the page that made the request. The Referer header allows a server to identify the page from which people visit it. With allowed referer settings, you can ensure that your video is only accessible from a specific server/host. You can specify multiple referrers using which you want your video to be accessible.
How to Allow Referrers for your websites?
To make Gumlet videos playable on specific websites, you must add every domain and subdomain where the videos will be embedded to your Gumlet video settings. Only the domains you list there will be allowed to load and play your Gumlet-hosted videos.
Note: You can also use a wildcard to allow videos to play on multiple subdomains.
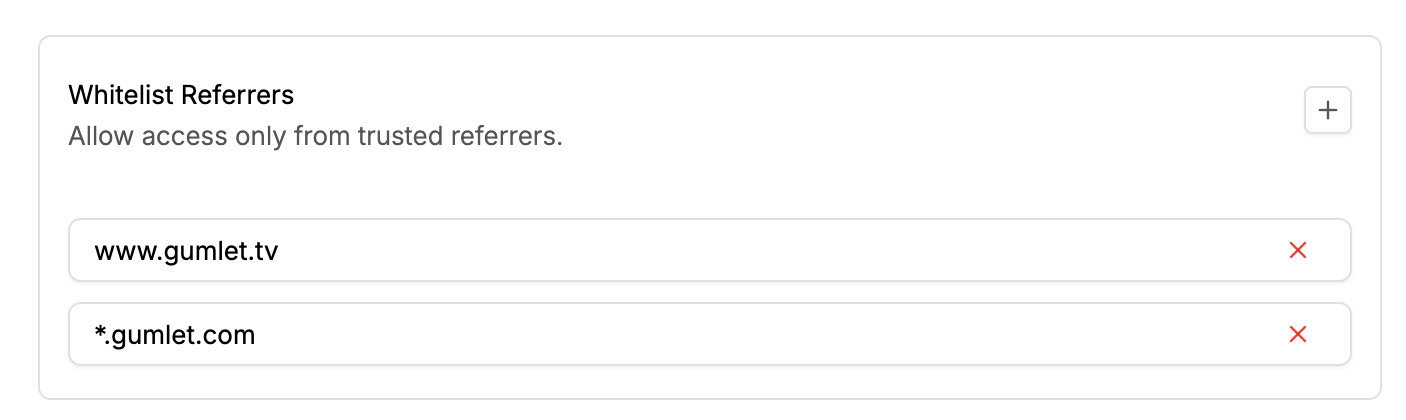
How to Whitelist an Android app?
To allow Gumlet to whitelist your Android app, add the app bundle name to the whitelist referrers input box. You can get the bundle ID from your developer or the app's URL on the Google Play Store.
For example - if the app URL is https://play.google.com/store/apps/details?id=com.google.android.calendar, the bundle ID would be com.google.android.calendar. Get the id parameter from the app URL.
How to Whitelist an iOS app?
To allow Gumlet to whitelist your iOS app, add the app bundle name to the whitelist referrers input box. You can get the bundle ID from your developer or follow the steps below.

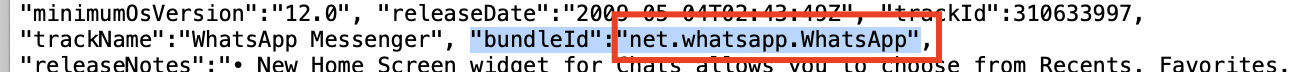
For example - if the app URL is https://apps.apple.com/us/app/whatsapp-messenger/id310633997, Copy the ID from the URL after the /id, i.e., the numeric part.
Navigate to https://itunes.apple.com/lookup?id={copied_id}, sample URL - https://itunes.apple.com/lookup?id=310633997. It will download a text file.
Open the text and copy the bundle ID as shown in the screenshot below:
If you have apps built with circle.so, whitelistcircle.soexplicitly with Gumlet.
If you want to whitelist multiple subdomains, you can use wildcard(*). For e.g., *.gumlet.com will allow you to play videos across all subdomains of Gumlet.com
If your apps do not send the x-requested-with header, you should send it explicitly.Sample header:
headers: { 'x-requested-with': "net.whatsapp.WhatsApp"}
Signed URL
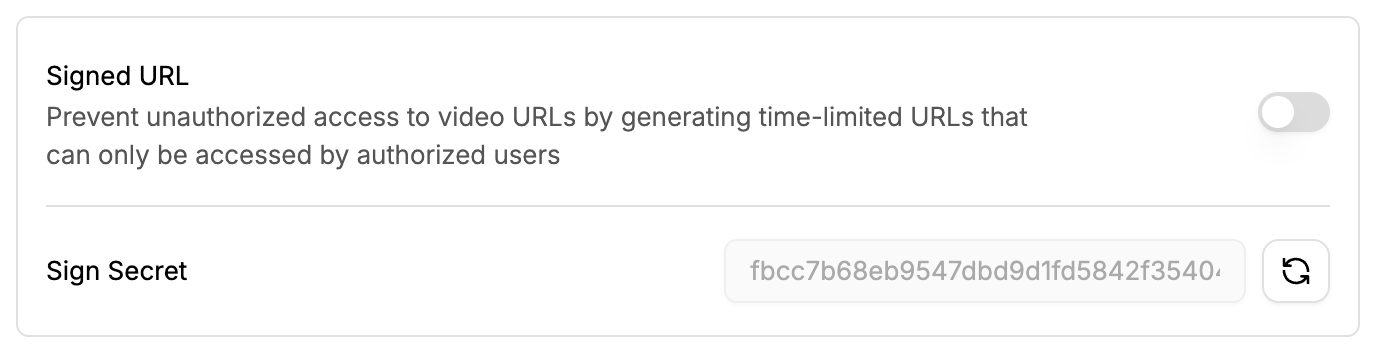
When enabled, this option provides a 16-byte hexadecimal sign secret key to generate a secure token and an expiration timestamp (Expiration time should be at least the duration of the Video Asset or the expected period). Video playback URLs under the video workspace will only be accessible with correctly generated tokens by the secret key and within the expiration time. When the signed URL expires, the URL will no longer be playable, even if playback has already started. The code snippets convert the ordinary Gumlet playback URL into a signed URL.
The code snippets below are intended for the M3U8 and MPD formats:
var crypto = require('crypto');
// Gumlet Video Playback URL
var playBackUrl = "https://video.gumlet.io/5f462c1561cf8a766464ffc4/6192269e0822a81d955d1a4b/main.m3u8";
// Secret key provided by Gumlet
var secret = "GNCP2ePfmdV3bHKqbiBAlXQXHKmI9+DZfLVptsvgUU4=";
secret = Buffer.from(secret, 'base64');
// expiration time in seconds
var tokenlifetime = 3600;
var expiration = Math.round(Date.now()/1000 + tokenlifetime);
var stringForTokenGeneration = playBackUrl.slice(23) + String(expiration);
var signature = crypto.createHmac('sha1', secret).update(stringForTokenGeneration).digest('hex');
console.log(`Signed Playback URL: ${playBackUrl}?token=${signature}&expires=${expiration}`);import hmac
from hashlib import sha1
from base64 import b64decode
from datetime import datetime, timedelta
# Gumlet Video Playback URL
playback_url = "https://video.gumlet.io/5f462c1561cf8a766464ffc4/6192269e0822a81d955d1a4b/1.m3u8"
# Secret key provided by Gumlet
secret = b"GNCP2ePfmdV3bHKqbiBAlXQXHKmI9+DZfLVptsvgUU4="
secret = b64decode(secret)
# expiration time in seconds
token_life_time = 3600;
expiration = datetime.now() + timedelta(seconds=token_life_time)
expiration = int(expiration.timestamp())
string_for_token_generation = playback_url[23:] + str(expiration)
string_for_token_generation = str.encode(string_for_token_generation)
signature = hmac.HMAC(secret, string_for_token_generation, sha1).digest().hex()
print("Token: {}".format(signature))
print("Signed Playback URL: {}?token={}&expires={}".format(playback_url, signature, expiration))require 'base64'
require 'openssl'
# Gumlet Video Playback URL
playback_url = "https://video.gumlet.io/5f462c1561cf8a766464ffc4/6192269e0822a81d955d1a4b/1.m3u8"
# Secret key provided by Gumlet
secret = "GNCP2ePfmdV3bHKqbiBAlXQXHKmI9+DZfLVptsvgUU4="
secret = Base64.decode64(secret)
# expiration time in seconds
token_life_time = 3600
expiration = Time.now.to_i + token_life_time
string_for_token_generation = playback_url.slice(23, playback_url.length) + expiration.to_s
signature = OpenSSL::HMAC.hexdigest('sha1', secret, string_for_token_generation)
puts "Token: " + signature
puts "Signed Playback URL: " + playback_url + "?token=" + signature + "&expires=" + expirationThe code snippet below is intended for the embed code URL:
var crypto = require('crypto');
// Gumlet Video Playback URL
var host = "https://play.gumlet.io";
var playBackUrl = "/embed/6192269e0822a81d955d1a4b?watermark_text=test";
// Secret key provided by Gumlet
var secret = "GNCP2ePfmdV3bHKqbiBAlXQXHKmI9+DZfLVptsvgUU4=";
secret = Buffer.from(secret, 'base64');
// expiration time in seconds
var tokenlifetime = 3600;
var expiration = Math.round(Date.now()/1000 + tokenlifetime);
var stringForTokenGeneration = playBackUrl +`${playBackUrl.indexOf('?') !== -1 ? '&' : '?'}signed_expires=` + String(expiration);
var signature = crypto.createHmac('sha1', secret).update(stringForTokenGeneration).digest('hex');
console.log(`Signed Playback URL: ${host}${playBackUrl}${playBackUrl.indexOf('?') !== -1 ? '&' : '?'}signed_token=${signature}&signed_expires=${expiration}`);You can also create temper-prood dymanic watermark using the signed embed code.
Best practices for video protection
-
Start simple, then layer protections
Begin with the appropriate video privacy level, then add geo‑blocking and referrer whitelisting, and finally use signed URLs only when needed. -
Protect high‑value content more strictly
Use Unlisted or Private privacy, combine it with Allow Referrers, and add Signed URLs for paid, internal, or sensitive videos. -
Keep your allowed list up to date
Whenever you add new domains or mobile apps, remember to update your Allow Referrers configuration so legitimate viewers are not blocked. -
Test from real viewer environments
After changing geo‑blocking or referrer rules, test playback from different countries (via VPN) and from all your key domains and apps. -
Monitor errors and viewer feedback
Watch for spikes in failed plays in analytics and be ready to relax overly strict rules if genuine users are getting blocked.
Updated about 1 month ago